
Help Desk Support for Your Bay Area Business
Don’t let tech issues slow you down. You can count on our team for fast, dependable troubleshooting and guidance whenever something goes wrong.
15-Minute Response Time You Can Rely On
When issues arise, you don’t have time to wait. Our guaranteed 15-minute response time ensures your requests are acknowledged quickly, helping you minimize downtime and keep your business running smoothly.

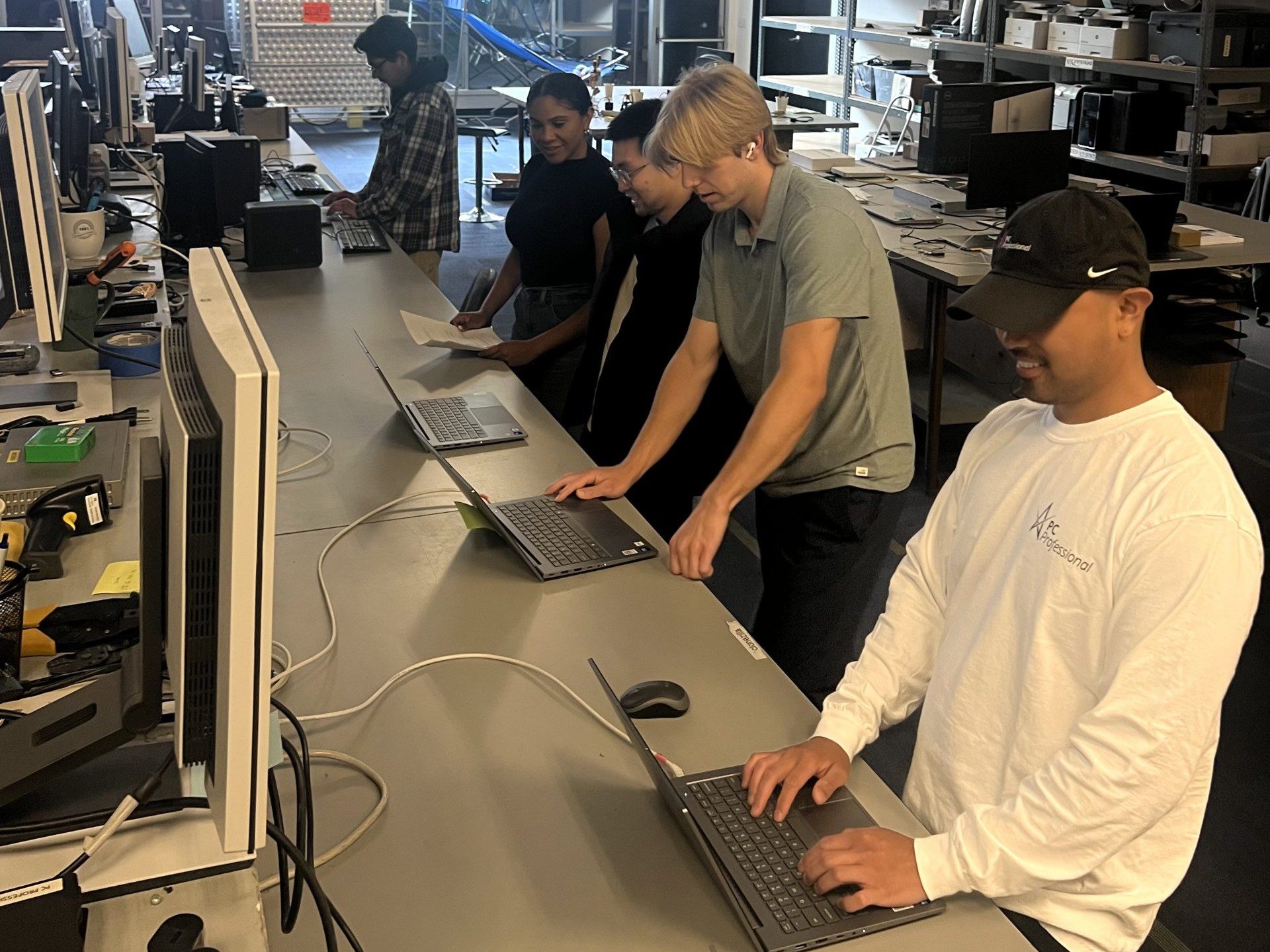
Help Desk Support That Keeps Your Team Moving
When your team needs help, our help desk is right there for you. You get timely, expert support that minimizes disruptions and keeps work on track.
Technical Support & Troubleshooting
We tackle every IT challenge, from protecting your data to keeping your devices, networks, and software working efficiently.
Network & System Management
Keep your WiFi network, servers, and devices running smoothly with assessments, proactive monitoring, and maintenance.
Software Administration
Keep Office 365 and other software running smoothly, so your team has the tools they need, when they need them.
Onboarding
We make employee onboarding effortless by setting up accounts, emails, access, and all necessary IT equipment.
Remote Assistance
Remote IT assistance keeps your team productive—securely access office computers, configure VPNs, and perform maintenance.
Ticketing System
Submit tickets for assistance easily and receive help online, over the phone, or in person.
Partner with a team who will be with you every step of the way.
